PixieBrix integrates with





%201.svg)
+1000s more












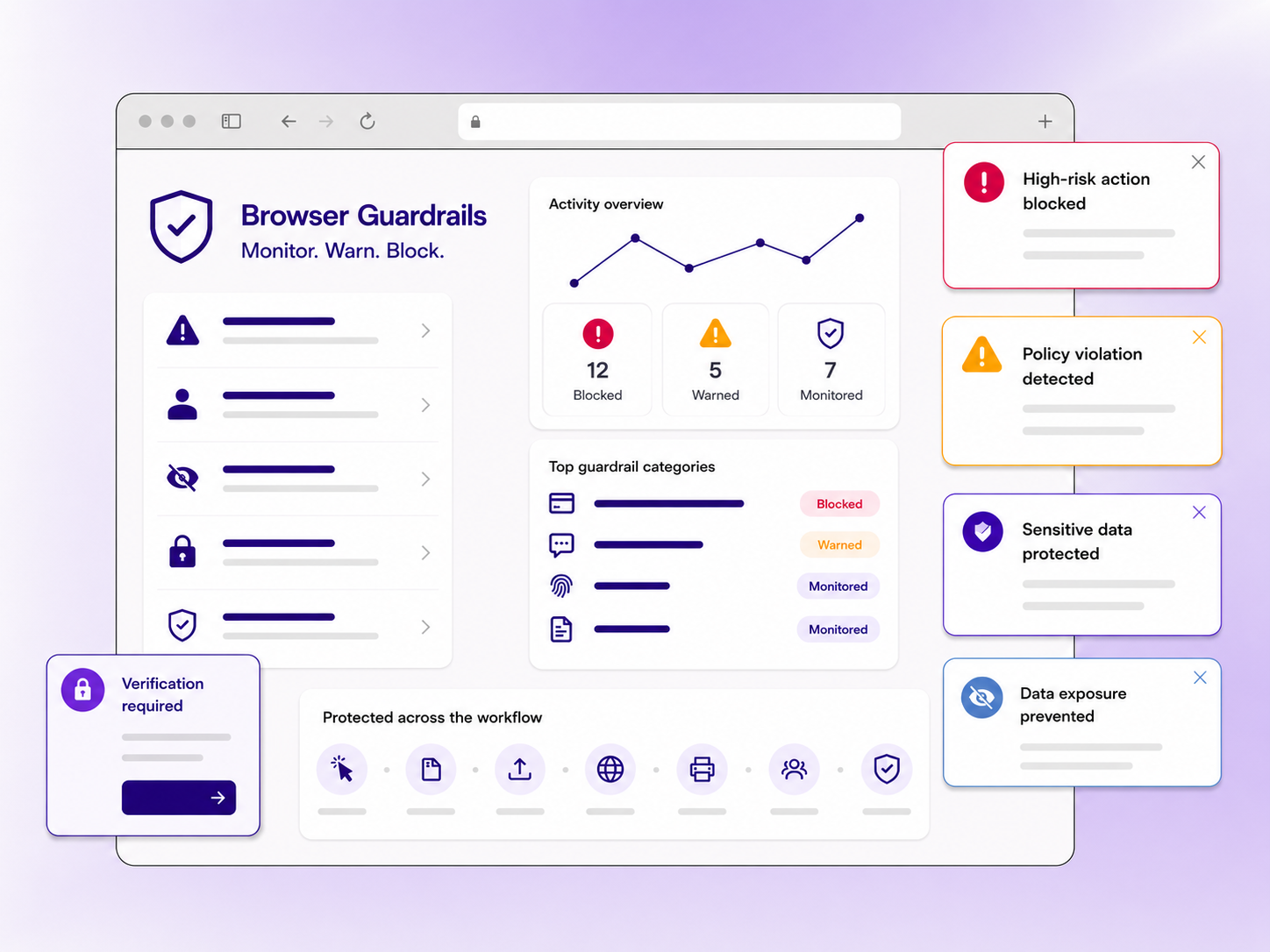















Secure enterprise browsers replace the browser itself, which often requires user retraining and migration. PixieBrix runs as an extension inside the browsers your team already uses, layering guardrails into existing workflows without forcing a switch.
DLP catches files crossing network or endpoint boundaries. PixieBrix sits inside the browser, catching risky actions, paste events, and policy violations in the flow of work — before they ever become DLP events
Yes. PixieBrix runs as a browser extension on top of the DOM, so it works with any browser-based application — third-party SaaS, internal apps, or custom-built tools.
On-device. The PixieBrix extension processes data inside the browser, and nothing leaves the device unless you configure telemetry to flow to your SIEM or observability stack.
Most guardrails can be built and deployed in minutes using low-code or AI coding — no sandbox or test environment required.
Yes. PixieBrix detects paste events to non-sanctioned domains (including ChatGPT, Claude, and other public AI tools), can surface sanctioned alternatives in-app, and can block high-risk pastes entirely.
Yes. PixieBrix can be deployed and managed through Chrome and Edge enterprise policies, Group Policy, Intune, JAMF, and other standard MDM tools.
Yes. PixieBrix is SOC 2 Type II certified. Full security documentation — penetration tests, architecture reviews, and policies — is available on request.

